Remko Weijnen's Blog (Remko's Blog)
About Virtualization, VDI, SBC, Application Compatibility and anything else I feel like
A few days ago I needed to test a few things on a Windows XP Workstation running under a regular user account.
I wanted to verify if some files and registry keys existed but Group Policies were in place that denied me access to the command prompt and regedit.
While this may be a good thought to secure the pc it is not very convenient if you need to verify some settings.
For that purpose I created patched versions of the Windows Server 2003 command prompt and regedit utilities.
They are patched to ignore the Group Policy settings and I usually place them in some share, secured by NTFS permissions.
You can read about it in my post: Registry editing has been disabled by your administrator (not anymore!).
However due to kernel differences you cannot use the Windows 2003 cmd.exe on Windows XP (you can do it the other way round btw). So I decided to create a patched version of the XP version as well.
I thought it might be interesting to show you how it’s done so here we go:
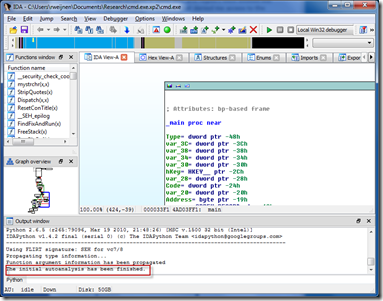
First we open up cmd.exe in Ida Pro:
On the first screen you can accept the defaults:
Wait until the Auto Analyses has finished, this may take a little while:
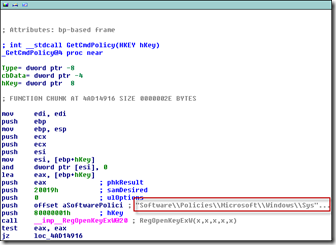
Now go to the Functions Window and sort on Function name and look for any functions that may have something to do with the policy check.
Or use the Search function (ALT-T) like I did:
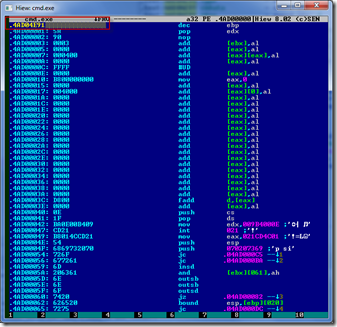
The first and only hit is a function Called GetCmdPolicy which sounds like what we need. DoubleClick on the function name to go to the Disassembly:
We can quickly see that this code is opening the Policies key:
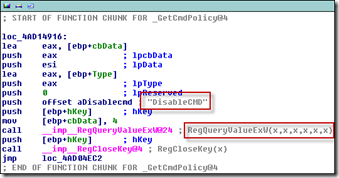
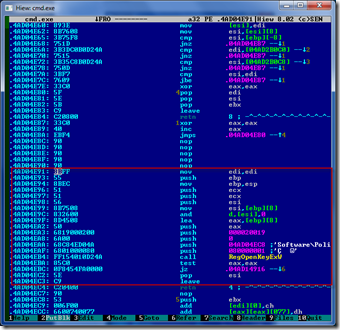
And in the next block we can see that the DisableCMD value is checked:
Now we will patch this function to return 0 which will make it always start, regardless of the value of the DisableCMD value.
Press the Space Bar to go to Ida’s Flat View and note down the Address of this function:
Now we are going to use a Hex Editor to create the Patch.
I use Hiew in this example because it can Disassemble and Assemble so it’s a very convenient tool for this purpose.
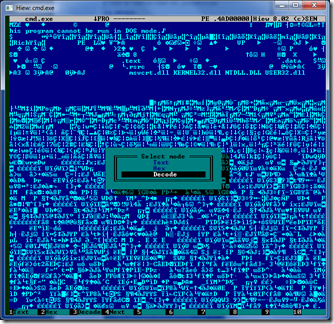
Open cmd.exe in Hiew and press F4 to change the Mode to Decode:
Press F5 (Goto) and enter a dot (.) and the Address from Ida:
Now we see the same Disassembly as in Ida:
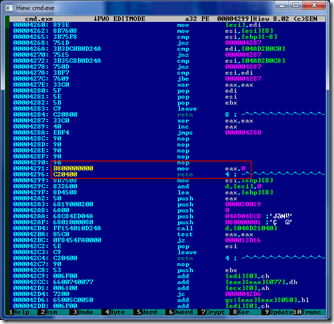
Now Press F3 to go to Edit Mode, followed by F2 to Select Assembly mode.
In the window that appears change mov edi,edi to mov eax,0 and press Enter:
Then change push ecx to ret 4 and press Enter:
Press Escape to Exit the Edit mode, we have now made the following changes:
Finally press F9 to save the changes and F10 to quit and we’re done!
And for the Lazy People the patched cmd.exe can be downloaded, usage is at your own risk:
Patched XP Command Prompt (2529 downloads )Profile
Top Posts
- Query Active Directory from Excel
- RNS 510 Startup Logo–My thoughts
- Adding a hidden Exchange mailbox to Outlook
- How rdp passwords are encrypted
- Get Actual CPU Clock Speed with PowerShell
- ClickOnce Applications in Enterprise Environments
- VW RNS 510 Navigation Startup Pictures
- Unattended Installation of IBM System i Access for Windows
- Reading physical memory size from the registry
- Show Client IP Address when using NetScaler as a Reverse Proxy
Recent Comments
Featured Downloads
- AClientFix (13595 downloads )
- AddPrinter2.zip (12854 downloads )
- AdProps (12379 downloads )
- AdSample1 (11432 downloads )
- AMD Radeon Crimson ReLive (25398 downloads )
- Atheros Driver (34019 downloads )
- AutoLogonXP 1.0 (11404 downloads )
- CDZA (9560 downloads )
- ChDrvLetter.zip (11217 downloads )
- ChDrvLetter.zip (14356 downloads )
Blogroll
- Andrew Morgan
- Arnout’s blog
- Assa’s Blog
- Barry Schiffer
- Delphi Praxis
- Ingmar Verheij
- Jedi Api Blog
- Jedi API Library
- Jeroen Tielen
- Kees Baggerman
Categories
- .NET (4)
- Active Directory (28)
- Altiris (36)
- App-V (1)
- Apple (5)
- Application Compatibility (11)
- Automotive (5)
- AWS (1)
- BootCamp (1)
- C# (6)
- C++ (2)
- Citrix (87)
- Delphi (61)
- Embedded (4)
- Exchange (16)
- General (71)
- iPhone (5)
- Java (8)
- Linux (1)
- Lync (2)
- NetScaler (1)
- Oracle (4)
- Other (1)
- Packaging (19)
- PowerShell (56)
- Programming (79)
- Quest (1)
- RES (7)
- script (22)
- ShareFile (1)
- SQL Server (10)
- Strange Error (3)
- Terminal Server (68)
- ThinApp (3)
- ThinKiosk (1)
- Ubuntu (1)
- Unattended Installation (19)
- Uncategorized (51)
- UWP (2)
- Vista (37)
- Visual Studio (1)
- VMWare (26)
- Windows 10 (2)
- Windows 2003 (30)
- Windows 2008 (37)
- Windows 2008 R2 (16)
- Windows 2012 (2)
- Windows 7 (30)
- Windows 8 (4)
- Windows Internals (12)
- Windows XP (16)
Archives
- February 2023 (1)
- October 2022 (3)
- July 2022 (1)
- June 2022 (2)
- October 2019 (1)
- March 2018 (1)
- January 2018 (4)
- December 2017 (3)
- April 2017 (1)
- March 2017 (5)
- February 2017 (4)
- May 2016 (3)
- March 2016 (1)
- October 2015 (2)
- September 2015 (1)
- January 2015 (1)
- August 2014 (1)
- July 2014 (8)
- May 2014 (1)
- November 2013 (1)
- October 2013 (2)
- September 2013 (3)
- August 2013 (4)
- June 2013 (2)
- May 2013 (3)
- April 2013 (5)
- March 2013 (5)
- February 2013 (1)
- January 2013 (5)
- December 2012 (9)
- November 2012 (3)
- October 2012 (3)
- August 2012 (4)
- July 2012 (2)
- June 2012 (1)
- May 2012 (6)
- March 2012 (13)
- February 2012 (12)
- January 2012 (9)
- December 2011 (9)
- November 2011 (4)
- October 2011 (5)
- September 2011 (10)
- August 2011 (10)
- July 2011 (2)
- June 2011 (8)
- May 2011 (12)
- April 2011 (4)
- March 2011 (14)
- February 2011 (8)
- January 2011 (32)
- December 2010 (23)
- November 2010 (19)
- October 2010 (10)
- September 2010 (6)
- August 2010 (1)
- July 2010 (1)
- June 2010 (6)
- March 2010 (7)
- February 2010 (3)
- December 2009 (3)
- November 2009 (11)
- September 2009 (2)
- July 2009 (1)
- June 2009 (5)
- May 2009 (1)
- April 2009 (2)
- March 2009 (3)
- February 2009 (6)
- January 2009 (3)
- December 2008 (8)
- November 2008 (5)
- October 2008 (3)
- September 2008 (3)
- August 2008 (3)
- June 2008 (6)
- May 2008 (2)
- April 2008 (3)
- March 2008 (5)
- January 2008 (3)
- December 2007 (3)
- November 2007 (13)
- October 2007 (10)




One Response for "Windows XP Cmd Prompt Patch"
[…] Dit blogartikel was vermeld op Twitter door Jim Moyle, Helge Klein en -b-, Remko Weijnen. Remko Weijnen heeft gezegd: Blogged: The #Windows XP cmd.exe patch as promised a while ago, includes a howto! http://bit.ly/g0UEDQ […]
Leave a reply