Remko Weijnen's Blog (Remko's Blog)
About Virtualization, VDI, SBC, Application Compatibility and anything else I feel like
Yesterday I was troubleshooting an application that was migrated to Citrix XenApp.
The application is able to use a high precision scale which is attached to the client pc’s com port. This com port is redirected to XenApp.
While testing users reported several issues, let’s have a look at them.
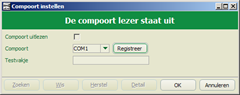
Error configuring COM Port
Within the application the comport to which the scale is connected must be configured:
After pressing "Registreer" to register the new com port the following error message was shown
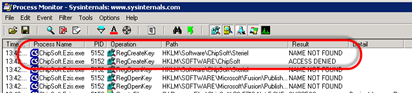
A Process Monitor trace quickly revealled the problem, the application wants to store the configuration in the HKLM hive:
We could circumvent this error by pre-creating this registry key and adding Modify permissions to it. However this presents us with a new issue in multi-user environments such as XenApp: if one user actives this setting, it is activated for all users on the same server.
Registry Redirection
That’s why I figured that redirecting this particular registry key from HKLM to HKCU would be the best solution.
I first tried the VirtualRegistry but even though AcLayers.dll was on stack right before the call to RegCreateKeyExW the redirection didn’t work.
Time to bring in other tools!
Disassemble
Regular readers probably expect me to launch Ida Pro now but I saw that mscorwks.dll was on stack in the Process Monitor trace. This means that we are dealing with a .NET application for which .NET Reflector is a better choice.
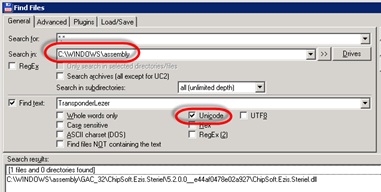
But before starting Reflector I needed to know what file(s) I needed to analyze. I used Total Commander, one of my favourite tools, to search for the word TransponderLezer since this is the registry value that contains the com port number.
I got no hits in the application’s program folder so I repeated the search but this time searching for Unicode. Again no hits, so I repeated the search on the .NET Assembly folder (C:\Windows\Assembly) and with Unicode I had a hit:
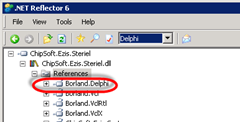
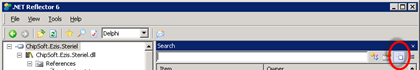
I loaded the file "ChipSoft.Ezis.Steriel.dll" in Reflector and expanded it. Under References I noticed Borland.Delphi which tells me the application is written in Delphi.NET. Therefore I set the language in Reflector to Delphi:
Note that choosing the same language as the application was built in is not required. Since .NET code is compiled to intermediate code (IL) you could also select C# or VB.NET. However I think that selecting the original language might make it easier to read code that calls into the language’s RTL.
I enabled Search via the View Menu and selected the Search String or Constant option:
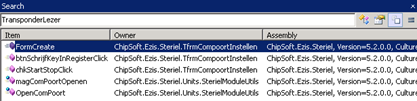
I searched for TransponderLezer again and that yielded a couple of results:
I opened the one called btnSchrijfKeyInRegisterClick (Write Key to Registry) and watched the Disassembly output:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 | procedure TfrmCompoortInstellen.btnSchrijfKeyInRegisterClick(Sender: TObject); begin if (System.@WStrCmp(self.cmbComPoort.Text, '') <> 0) then begin SterielModuleUtils.schrijfRegisterSleutelString('Software\ChipSoft\Steriel', 'TransponderLezer', self.cmbComPoort.Text); self.chkStartStop.Checked := false; self.chkStartStopClick(Sender); if (System.@WStrCmp(self.cmbComPoort.Text, 'Wissen') <> 0) then begin self.chkStartStop.Checked := true; self.chkStartStopClick(Sender) end end end; |
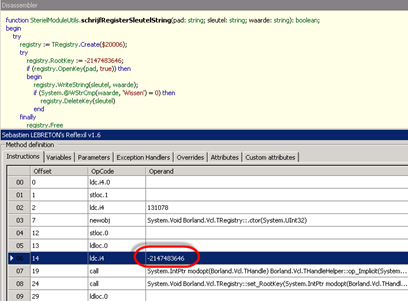
This procedure calls into a function named schrijfRegisterSleutelString. Let’s have a look at that one:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 | function SterielModuleUtils.schrijfRegisterSleutelString(pad: string; sleutel: string; waarde: string): boolean; begin try registry := TRegistry.Create($20006); try registry.RootKey := -2147483646; if (registry.OpenKey(pad, true)) then begin registry.WriteString(sleutel, waarde); if (System.@WStrCmp(waarde, 'Wissen') = 0) then registry.DeleteKey(sleutel) end finally registry.Free end except on obj1: TObject do begin obj2 := System.@ExceptObject := obj1; Msgbox.ErrorMsg('Het schrijven van de sleutel in het register is niet gelukt. Controleer of u schrijfrechten heeft, en probeer het opnieuw'); System.@ExceptObject := nil end end; begin Result := false; exit end end; |
The interesting part is the marked line, the value -2147483646 is passed as the RootKey. The corresponding hex value is 80000002 which is the same as the constant value for HKEY_LOCAL_MACHINE:
1 2 | #define HKEY_LOCAL_MACHINE (( HKEY ) (ULONG_PTR)((LONG)0x80000002) ) #define HKEY_CURRENT_USER (( HKEY ) (ULONG_PTR)((LONG)0x80000001) ) |
So if we edit this value to the constant value of HKEY_CURRENT_USER we have redirected the registry key from HKLM to HKCU.
Modifying the binary
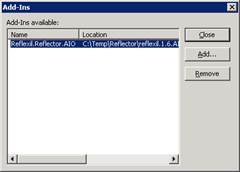
To do this we need to download an Add-In for Reflector called Reflexil. To activate it, go to View | Add-Ins:
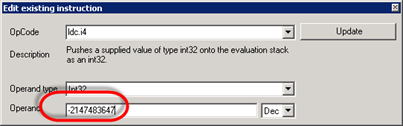
After adding it, choose Tools | Reflexil 1.6 to open Reflexil’s view. Select the line you want to edit, in my case line 06.
Right-click and choose Edit. The new value is the Decimal value of the HKEY_CURRENT_USER constant which is -2147483647:
Press update and make the same change to the read function which is called leesRegisterSleutelString.
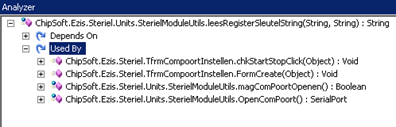
It’s a good idea to check if other parts of the code are calling into these functions. You can do this by Right-clicking on the function in the left tree view and selecting Analyze.
In the Analyzer expand the "Used By" node, in my case only code related to the com port is affected. Therefore I consider the change to be safe:
Committing changes
Finally we can save the modified executable to disk by Right-clicking on the file in the left treeview and selecting Reflexil | Save As.
Fixed?
Usually I end my blogs with a sentence like: and that fixed it!
However now that the scale is working, testers have reported issues when they roam their XenApp session to another pc.
If the application is connected to the scale and the session is reconnected to a client pc without scale the application presents an error message which is acceptable.
But when you later on reconnect to a client with an attached scale the application crashes.
So in the end this fix did not go into production, not even as temporary workaround. We are going to contact the vendor and request a fix for both issues.
Profile
Top Posts
- Query Active Directory from Excel
- RNS 510 Startup Logo–My thoughts
- Adding a hidden Exchange mailbox to Outlook
- How rdp passwords are encrypted
- Get Actual CPU Clock Speed with PowerShell
- ClickOnce Applications in Enterprise Environments
- VW RNS 510 Navigation Startup Pictures
- Unattended Installation of IBM System i Access for Windows
- Reading physical memory size from the registry
- Show Client IP Address when using NetScaler as a Reverse Proxy
Recent Comments
Featured Downloads
- AClientFix (13595 downloads )
- AddPrinter2.zip (12854 downloads )
- AdProps (12379 downloads )
- AdSample1 (11432 downloads )
- AMD Radeon Crimson ReLive (25220 downloads )
- Atheros Driver (34019 downloads )
- AutoLogonXP 1.0 (11404 downloads )
- CDZA (9560 downloads )
- ChDrvLetter.zip (11217 downloads )
- ChDrvLetter.zip (14356 downloads )
Blogroll
- Andrew Morgan
- Arnout’s blog
- Assa’s Blog
- Barry Schiffer
- Delphi Praxis
- Ingmar Verheij
- Jedi Api Blog
- Jedi API Library
- Jeroen Tielen
- Kees Baggerman
Categories
- .NET (4)
- Active Directory (28)
- Altiris (36)
- App-V (1)
- Apple (5)
- Application Compatibility (11)
- Automotive (5)
- AWS (1)
- BootCamp (1)
- C# (6)
- C++ (2)
- Citrix (87)
- Delphi (61)
- Embedded (4)
- Exchange (16)
- General (71)
- iPhone (5)
- Java (8)
- Linux (1)
- Lync (2)
- NetScaler (1)
- Oracle (4)
- Other (1)
- Packaging (19)
- PowerShell (56)
- Programming (79)
- Quest (1)
- RES (7)
- script (22)
- ShareFile (1)
- SQL Server (10)
- Strange Error (3)
- Terminal Server (68)
- ThinApp (3)
- ThinKiosk (1)
- Ubuntu (1)
- Unattended Installation (19)
- Uncategorized (51)
- UWP (2)
- Vista (37)
- Visual Studio (1)
- VMWare (26)
- Windows 10 (2)
- Windows 2003 (30)
- Windows 2008 (37)
- Windows 2008 R2 (16)
- Windows 2012 (2)
- Windows 7 (30)
- Windows 8 (4)
- Windows Internals (12)
- Windows XP (16)
Archives
- February 2023 (1)
- October 2022 (3)
- July 2022 (1)
- June 2022 (2)
- October 2019 (1)
- March 2018 (1)
- January 2018 (4)
- December 2017 (3)
- April 2017 (1)
- March 2017 (5)
- February 2017 (4)
- May 2016 (3)
- March 2016 (1)
- October 2015 (2)
- September 2015 (1)
- January 2015 (1)
- August 2014 (1)
- July 2014 (8)
- May 2014 (1)
- November 2013 (1)
- October 2013 (2)
- September 2013 (3)
- August 2013 (4)
- June 2013 (2)
- May 2013 (3)
- April 2013 (5)
- March 2013 (5)
- February 2013 (1)
- January 2013 (5)
- December 2012 (9)
- November 2012 (3)
- October 2012 (3)
- August 2012 (4)
- July 2012 (2)
- June 2012 (1)
- May 2012 (6)
- March 2012 (13)
- February 2012 (12)
- January 2012 (9)
- December 2011 (9)
- November 2011 (4)
- October 2011 (5)
- September 2011 (10)
- August 2011 (10)
- July 2011 (2)
- June 2011 (8)
- May 2011 (12)
- April 2011 (4)
- March 2011 (14)
- February 2011 (8)
- January 2011 (32)
- December 2010 (23)
- November 2010 (19)
- October 2010 (10)
- September 2010 (6)
- August 2010 (1)
- July 2010 (1)
- June 2010 (6)
- March 2010 (7)
- February 2010 (3)
- December 2009 (3)
- November 2009 (11)
- September 2009 (2)
- July 2009 (1)
- June 2009 (5)
- May 2009 (1)
- April 2009 (2)
- March 2009 (3)
- February 2009 (6)
- January 2009 (3)
- December 2008 (8)
- November 2008 (5)
- October 2008 (3)
- September 2008 (3)
- August 2008 (3)
- June 2008 (6)
- May 2008 (2)
- April 2008 (3)
- March 2008 (5)
- January 2008 (3)
- December 2007 (3)
- November 2007 (13)
- October 2007 (10)


Leave a reply