Remko Weijnen's Blog (Remko's Blog)
About Virtualization, VDI, SBC, Application Compatibility and anything else I feel like
Archive for January, 2011
Determine the System Page Size
Author: Remko Weijnen24 Jan
Just a quick note: if you want to determine the page size of the OS (Windows) you can use the GetSystemInfo function.
Example:
1 2 3 4 5 6 | var SystemInfo: SYSTEM_INFO; PageSize: DWORD; begin GetSystemInfo(SystemInfo); PageSize := SystemInfo.dwPageSize; |
Note that MSDN recommends to use the GetNativeSystemInfo function when running in a 32 bit app on an x64 OS (and you can use the IsWow64Process function to determine that).
One example where you need to know the PageSize is when you want to create a Paging File using the NtCreatePagingFile function because this function requires that the MinimumSize and MaximumSize parameters are a multiple of the PageSize.
Some interesting links on the subject:
The case of the UPS discovery not working
Author: Remko Weijnen24 Jan
I am doing a project involving a Citrix Xenapp environment running on VMWare vSphere.
The physical machines are powered by two Eaton Uninterruptable Power Supplies that both a network card.
I received some documentation that describes how to implement automatic shutdown in a VMWare vSphere environment.
This documentation describes that a vSphere Management Assistant (vMA) must be deployed in which we need to install some software from Eaton.
I followed the documentation that even described the needed iptables rules needed for their software.
In the last step a discovery is done and the UPS is supposed to be found. And you have probably guessed by now: it didn’t!
At first I figured that maybe the iptables configuration was still too tight so I stopped the iptables service but that didn’t help.
Enumerating Session Processes with NtQuerySystemInformation
Author: daNIL20 Jan
As you may know, you can enumerate processes of a specific Terminal Server or Citrix session using the NtQuerySystemInformation function.
On x86 system the code below works fine:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 | var Status : NTSTATUS; RetLength : DWORD; SessionInfo : SYSTEM_SESSION_PROCESS_INFORMATION; CurrentProcess : PSystemProcesses; begin SessionInfo.SessionId := SessionId; SessionInfo.Buffer := nil; SessionInfo.SizeOfBuf := 0; Status := NtQuerySystemInformation(SystemSessionProcessesInformation, @SessionInfo, SizeOf(SessionInfo), @RetLength); while (Status = STATUS_INFO_LENGTH_MISMATCH) do begin SessionInfo.SizeOfBuf := RetLength; SessionInfo.Buffer := GetMemory(RetLength); try Status := NtQuerySystemInformation(SystemSessionProcessesInformation, @SessionInfo, SizeOf(SessionInfo), @RetLength); if NT_SUCCESS(Status) then begin CurrentProcess := SessionInfo.Buffer; while True do begin // Your code here if (CurrentProcess^.NextEntryDelta = 0) then Break; Cardinal(CurrentProcess) := Cardinal(CurrentProcess) + CurrentProcess^.NextEntryDelta; end; Exit; end; finally FreeMemory(SessionInfo.Buffer); end; end; SetLastError(RtlNtStatusToDosError(Status)); RaiseLastOSError; end; |
While this works fine on Windows XP and 2003 x86, it fails to work correctly on the x64 versions of Windows XP and 2003 (or maybe even higher).
The problem is that RetLength is always SizeOf(SYSTEM_SESSION_PROCESS_INFORMATION) and thus we are in an endless loop!
SasLibEx Screencast
Author: Remko Weijnen19 Jan
I just recorded a SasLibEx Screencast, it shows some of the very powerfull features of SasLibEx.
The following features are shown:
- Simulate Ctrl Alt Del (Secure Attention Sequence)
- Cancel Ctrl Alt Del
- Lock Workstation
- Unlock Workstation (without credentials)
- Disable Ctrl Alt Del
- Enable Ctrl Alt Del again
- Cancel pending UAC request
- Is Desktop Locked
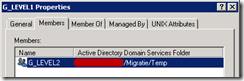
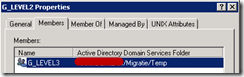
Recursive Groups #2
Author: Remko Weijnen18 Jan
In my previous post I explained how to get the recursive group membership with a very simple Powershell Script.
Commenter Michel thought that the script only tested one level deep but it doesn’t.
But let’s prove that!
Create 3 Global Groups in your Active Directory and name them Level1, 2 and 3:
Make Level3 a Member of Level 2 and make Level a member of Level 1 and finally add an account to the Level 3 group:
Kofax VRS Unattended Install
Author: Remko Weijnen18 Jan
Recently I needed to create an Unattended Install for an application that uses a piece of software (for scanning) called Kofax VRS.
This Kofax software comes with an .msi file but there was no documentation on the install options.
In fact it didn’t seem like the Vendor anticipated on an Unatttended Install.
I browsed in the msi file using Microsoft’s Orca tool and tried some of the properties I found in the public properties table.
Recursive group Membership in Powershell
Author: Remko Weijnen18 Jan
In this post I will show an easy way to get the recursive group membership for the current user.
I use this in a logon script to handle certain tasks based on group membership.
Most scripts I see for this task do a manual recursive enumeration but in a large environment this could be very slow.
A better way would be to use the tokenGroups attribute of the Active Directory user object.
The tokenGroups attribute is an array of SIDs computed by Active Directory and is used to verify user access.
We need to translate these SIDs to their sAMAccountNames to get the actual group names.
In unmanaged code this could be accomplished by calling the DsCrackNames API or the IADsNameTranslate interface.
The case of the Annotations Toolbar
Author: Remko Weijnen17 Jan
I got some interesting questions from a user today regarding TIFF images on a Windows 2003 based Citrix environment.
This user has an application that works with scanned documents and for each document exists both a pdf and a tiff version in the application.
By default the TIF (and TIFF) file extensions are linked to the Windows Picture and Fax Viewer in Windows 2003.
The user told me that some time ago she had an extra toolbar where she could perform some extra operations such as making a selection on TIFF images.
At some point in time this mysterious Toolbar disappeared and she was never able to get it back. She reported this to the helpdesk and the system administrator but they were unable to resolve this.
I hadn’t hear of this toolbar before but a Google Search led me to this page which explains the toolbar in question which is called the Annotation Toolbar.
Another packaging challenge
Author: Remko Weijnen17 Jan
Another post on something that happened last week, this time it’s about a Java based Application again.
This particular application wanted to download three DLL’s from the Webserver to the Java bin directory.
This presents us with several issues on a multi user server such as a Citrix of Terminal Server:
- The user does not have write permissions in this directory
- If we we give the user write permissions here what happens when the DLL’s are in use by another user?
I assumed that if I preinstalled the DLL’s the application wouldn’t try to overwrite them but that didn’t work.
Then I monitored with Process Monitor if the Application wrote some kind of check file but at first I didn’t find anything.
So I decided to use the CorrectFilePaths shim to redirect the DLL’s to the user’s homedirectory (see Using the CorrectFilePaths shim to redirect an ini file to a writable location for an explanation).
Troubleshoot CorrectFilePath shim
Author: Remko Weijnen16 Jan
A few days ago I was packaging an application that was writing an INI file in the application directory.
If you have read my earlier article, Using the CorrectFilePaths shim to redirect an ini file to a writable location, then you will probably think: create a nice shim and redirect that ini file!
But this application had a few challenges, the first being that it writes %COMPUTERNAME%.INI. The application’s developer probably assumed that a user is bound to one pc and that no other user’s use that pc.
To solve it we we need to catch all possible computer names (it would be nice if the CorrectFilePaths shims was able to accept wildcards and environment variables).
But it doesn’t so it means we have to add a parameter for each possible computer name. In my case that was doable because I have only 8 Citrix servers.
So I created a Fix using the Application Compatibility Manager as described in my previous post.
However it didn’t work, so I started to trace what happens.
Profile
Top Posts
- Query Active Directory from Excel
- RNS 510 Startup Logo–My thoughts
- Adding a hidden Exchange mailbox to Outlook
- How rdp passwords are encrypted
- Get Actual CPU Clock Speed with PowerShell
- ClickOnce Applications in Enterprise Environments
- VW RNS 510 Navigation Startup Pictures
- Unattended Installation of IBM System i Access for Windows
- Reading physical memory size from the registry
- Show Client IP Address when using NetScaler as a Reverse Proxy
Recent Comments
Featured Downloads
- AClientFix (13595 downloads )
- AddPrinter2.zip (12854 downloads )
- AdProps (12379 downloads )
- AdSample1 (11432 downloads )
- AMD Radeon Crimson ReLive (31904 downloads )
- Atheros Driver (34019 downloads )
- AutoLogonXP 1.0 (11404 downloads )
- CDZA (9560 downloads )
- ChDrvLetter.zip (11217 downloads )
- ChDrvLetter.zip (14356 downloads )
Blogroll
- Andrew Morgan
- Arnout’s blog
- Assa’s Blog
- Barry Schiffer
- Delphi Praxis
- Ingmar Verheij
- Jedi Api Blog
- Jedi API Library
- Jeroen Tielen
- Kees Baggerman
Categories
- .NET (4)
- Active Directory (28)
- Altiris (36)
- App-V (1)
- Apple (5)
- Application Compatibility (11)
- Automotive (5)
- AWS (1)
- BootCamp (1)
- C# (6)
- C++ (2)
- Citrix (87)
- Delphi (61)
- Embedded (4)
- Exchange (16)
- General (71)
- iPhone (5)
- Java (8)
- Linux (1)
- Lync (2)
- NetScaler (1)
- Oracle (4)
- Other (1)
- Packaging (19)
- PowerShell (56)
- Programming (79)
- Quest (1)
- RES (7)
- script (22)
- ShareFile (1)
- SQL Server (10)
- Strange Error (3)
- Terminal Server (68)
- ThinApp (3)
- ThinKiosk (1)
- Ubuntu (1)
- Unattended Installation (19)
- Uncategorized (51)
- UWP (2)
- Vista (37)
- Visual Studio (1)
- VMWare (26)
- Windows 10 (2)
- Windows 2003 (30)
- Windows 2008 (37)
- Windows 2008 R2 (16)
- Windows 2012 (2)
- Windows 7 (30)
- Windows 8 (4)
- Windows Internals (12)
- Windows XP (16)
Archives
- February 2023 (1)
- October 2022 (3)
- July 2022 (1)
- June 2022 (2)
- October 2019 (1)
- March 2018 (1)
- January 2018 (4)
- December 2017 (3)
- April 2017 (1)
- March 2017 (5)
- February 2017 (4)
- May 2016 (3)
- March 2016 (1)
- October 2015 (2)
- September 2015 (1)
- January 2015 (1)
- August 2014 (1)
- July 2014 (8)
- May 2014 (1)
- November 2013 (1)
- October 2013 (2)
- September 2013 (3)
- August 2013 (4)
- June 2013 (2)
- May 2013 (3)
- April 2013 (5)
- March 2013 (5)
- February 2013 (1)
- January 2013 (5)
- December 2012 (9)
- November 2012 (3)
- October 2012 (3)
- August 2012 (4)
- July 2012 (2)
- June 2012 (1)
- May 2012 (6)
- March 2012 (13)
- February 2012 (12)
- January 2012 (9)
- December 2011 (9)
- November 2011 (4)
- October 2011 (5)
- September 2011 (10)
- August 2011 (10)
- July 2011 (2)
- June 2011 (8)
- May 2011 (12)
- April 2011 (4)
- March 2011 (14)
- February 2011 (8)
- January 2011 (32)
- December 2010 (23)
- November 2010 (19)
- October 2010 (10)
- September 2010 (6)
- August 2010 (1)
- July 2010 (1)
- June 2010 (6)
- March 2010 (7)
- February 2010 (3)
- December 2009 (3)
- November 2009 (11)
- September 2009 (2)
- July 2009 (1)
- June 2009 (5)
- May 2009 (1)
- April 2009 (2)
- March 2009 (3)
- February 2009 (6)
- January 2009 (3)
- December 2008 (8)
- November 2008 (5)
- October 2008 (3)
- September 2008 (3)
- August 2008 (3)
- June 2008 (6)
- May 2008 (2)
- April 2008 (3)
- March 2008 (5)
- January 2008 (3)
- December 2007 (3)
- November 2007 (13)
- October 2007 (10)