Remko Weijnen's Blog (Remko's Blog)
About Virtualization, VDI, SBC, Application Compatibility and anything else I feel like
Archive for March, 2017
Where does the Citrix Linux VDA store settings?
Author: Remko Weijnen23 Mar
 I recently (well today really) started playing with the Citrix Linux VDA. I took Ubuntu to test because I happen to like Ubuntu.
I recently (well today really) started playing with the Citrix Linux VDA. I took Ubuntu to test because I happen to like Ubuntu.
I didn’t get it to work correctly right away though and during troubleshooting I wanted to know where the VDA is storing it’s settings.
I found the following file /etc/xdl/ctx-vda.confwith the following contents:
On forbes.com, Cookies and Ads
Author: Remko Weijnen14 Mar
Even though I try not to visit the forbes.com site anymore due to their heavy usages of ads, anti adblocker and overwhelming number of cookies they’re trying to push, sometimes however I accidentally follow a tweet that leads to forbes.com and just notice it to late.
Besides wasting your bandwidth, mobile data and especially time there have been a few occasions were the forbes.com page was actually serving malware from their adfeeds.
It annoys me bigtime so let’s “fix” this:
First thing that happens upon visiting the forbes site is that you get a blurred background with a random ad or quote of the day and you need to press Continue to article:
If you open the Developer console in Chrome (Application tab) you can see that Forbes uses a cookie that expires in 24 hours. This cookie make sure that you don’t see the “welcome” ad for 24 hours:
Modifying a .NET Application
Author: Remko Weijnen14 Mar
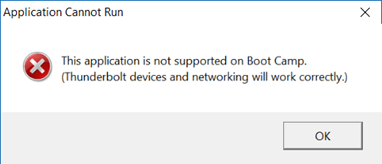
I will explain why in a seperate post, but on my MacBook Pro I wanted to use the Intel Thunderbolt driver under BootCamp instead of the ones supplied by Apple.
The Thunderbolt control program however refused with the following error message:
It’s really beyond me why Intel would deliberately block their Thunderbolt software on Apple hardware (under Windows). Believing this was just a simple hardcoded hardware check rather than any hardware issue that would prevent the drivers to work I proceeded into finding where the check takes place.
Convert Executable to PowerShell
Author: Remko Weijnen13 Mar
Recently I stumbled upon an executable that appeared to be a PowerShell script converted into an executable.
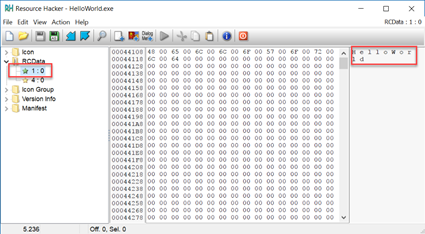
I was curious to the actual script so I decided to have a look and see how I could convert the executable back into PowerShell.
Having seen similar techniques to turn vb scripts and java jar’s into executables I first looked if this particular executable was simply carrying the payload in the resource section.
I opened the executable with Resource Hacker and saw 2 resources (note that I am using a simple HelloWorld executable here in the screenshots). The first resource, named 1, is clearly a Unicode string with the title:
Split a string by dollar sign ($) in PowerShell
Author: Remko Weijnen13 Mar
Just a very quick post (more like a note to self) but I wanted to split a string with the $ sign in PowerShell:
1 | 'one$two$three$four$five' -split '$' |
Took me a little while to realize that this doesn’t work as the split operator in Windows PowerShell uses a regular expression in the delimiter, rather than a simple character.
The easy fix is to Escape the $ sign with a backslash:
1 | 'one$two$three$four$five' -split '\$' |
Or alternatively use the SimpleMatch option:
1 | 'one$two$three$four$five' -split '$', 0, "SimpleMatch" |
The 0 represents the “return all” value of the Max-substrings parameter. You can use options, such as SimpleMatch, only when the Max-substrings value is specified.
Profile
Top Posts
- Query Active Directory from Excel
- RNS 510 Startup Logo–My thoughts
- Adding a hidden Exchange mailbox to Outlook
- How rdp passwords are encrypted
- Get Actual CPU Clock Speed with PowerShell
- ClickOnce Applications in Enterprise Environments
- VW RNS 510 Navigation Startup Pictures
- Unattended Installation of IBM System i Access for Windows
- Reading physical memory size from the registry
- Show Client IP Address when using NetScaler as a Reverse Proxy
Recent Comments
Featured Downloads
- AClientFix (13595 downloads )
- AddPrinter2.zip (12854 downloads )
- AdProps (12379 downloads )
- AdSample1 (11432 downloads )
- AMD Radeon Crimson ReLive (29920 downloads )
- Atheros Driver (34019 downloads )
- AutoLogonXP 1.0 (11404 downloads )
- CDZA (9560 downloads )
- ChDrvLetter.zip (11217 downloads )
- ChDrvLetter.zip (14356 downloads )
Blogroll
- Andrew Morgan
- Arnout’s blog
- Assa’s Blog
- Barry Schiffer
- Delphi Praxis
- Ingmar Verheij
- Jedi Api Blog
- Jedi API Library
- Jeroen Tielen
- Kees Baggerman
Categories
- .NET (4)
- Active Directory (28)
- Altiris (36)
- App-V (1)
- Apple (5)
- Application Compatibility (11)
- Automotive (5)
- AWS (1)
- BootCamp (1)
- C# (6)
- C++ (2)
- Citrix (87)
- Delphi (61)
- Embedded (4)
- Exchange (16)
- General (71)
- iPhone (5)
- Java (8)
- Linux (1)
- Lync (2)
- NetScaler (1)
- Oracle (4)
- Other (1)
- Packaging (19)
- PowerShell (56)
- Programming (79)
- Quest (1)
- RES (7)
- script (22)
- ShareFile (1)
- SQL Server (10)
- Strange Error (3)
- Terminal Server (68)
- ThinApp (3)
- ThinKiosk (1)
- Ubuntu (1)
- Unattended Installation (19)
- Uncategorized (51)
- UWP (2)
- Vista (37)
- Visual Studio (1)
- VMWare (26)
- Windows 10 (2)
- Windows 2003 (30)
- Windows 2008 (37)
- Windows 2008 R2 (16)
- Windows 2012 (2)
- Windows 7 (30)
- Windows 8 (4)
- Windows Internals (12)
- Windows XP (16)
Archives
- February 2023 (1)
- October 2022 (3)
- July 2022 (1)
- June 2022 (2)
- October 2019 (1)
- March 2018 (1)
- January 2018 (4)
- December 2017 (3)
- April 2017 (1)
- March 2017 (5)
- February 2017 (4)
- May 2016 (3)
- March 2016 (1)
- October 2015 (2)
- September 2015 (1)
- January 2015 (1)
- August 2014 (1)
- July 2014 (8)
- May 2014 (1)
- November 2013 (1)
- October 2013 (2)
- September 2013 (3)
- August 2013 (4)
- June 2013 (2)
- May 2013 (3)
- April 2013 (5)
- March 2013 (5)
- February 2013 (1)
- January 2013 (5)
- December 2012 (9)
- November 2012 (3)
- October 2012 (3)
- August 2012 (4)
- July 2012 (2)
- June 2012 (1)
- May 2012 (6)
- March 2012 (13)
- February 2012 (12)
- January 2012 (9)
- December 2011 (9)
- November 2011 (4)
- October 2011 (5)
- September 2011 (10)
- August 2011 (10)
- July 2011 (2)
- June 2011 (8)
- May 2011 (12)
- April 2011 (4)
- March 2011 (14)
- February 2011 (8)
- January 2011 (32)
- December 2010 (23)
- November 2010 (19)
- October 2010 (10)
- September 2010 (6)
- August 2010 (1)
- July 2010 (1)
- June 2010 (6)
- March 2010 (7)
- February 2010 (3)
- December 2009 (3)
- November 2009 (11)
- September 2009 (2)
- July 2009 (1)
- June 2009 (5)
- May 2009 (1)
- April 2009 (2)
- March 2009 (3)
- February 2009 (6)
- January 2009 (3)
- December 2008 (8)
- November 2008 (5)
- October 2008 (3)
- September 2008 (3)
- August 2008 (3)
- June 2008 (6)
- May 2008 (2)
- April 2008 (3)
- March 2008 (5)
- January 2008 (3)
- December 2007 (3)
- November 2007 (13)
- October 2007 (10)